When discussing physical security, there are several important talking points to consider. Here are some key points to include:
- Risk Assessment: Start by highlighting the importance of conducting a thorough risk assessment to identify potential vulnerabilities and threats to physical security. This assessment helps determine the level of security measures needed.
- Access Control: Discuss the significance of implementing access control systems, such as key cards, biometric authentication, or security personnel, to restrict unauthorized entry into sensitive areas. Emphasize the need to control and monitor access to ensure only authorized individuals have access.
- Perimeter Security: Talk about the significance of securing the perimeter of a facility, including fences, gates, and barriers. Highlight the need for surveillance cameras, motion sensors, and alarms to detect and deter intruders.
- Security Personnel: Discuss the role of trained security personnel in maintaining physical security. This may include security guards, receptionists, or other personnel responsible for monitoring and responding to security incidents.
- Surveillance Systems: Explain the importance of deploying a comprehensive surveillance system that includes cameras, video analytics, and recording capabilities. Discuss how these systems can deter criminal activity, provide evidence in case of incidents, and aid in investigations.
- Security Policies and Procedures: Highlight the significance of establishing clear security policies and procedures. Discuss the importance of training employees on these policies, including protocols for reporting security incidents, handling sensitive information, and responding to emergencies.
- Physical Barriers and Safeguards: Mention the use of physical barriers, such as reinforced doors, locks, and safes, to protect sensitive areas, equipment, and valuables. Explain how these measures can prevent unauthorized access or theft.
- Emergency Preparedness: Discuss the need for developing emergency response plans, including evacuation procedures, fire safety measures, and protocols for handling natural disasters or other crises. Emphasize the importance of regular drills and training sessions.
- Visitor Management: Highlight the significance of implementing visitor management protocols, including sign-in procedures, visitor badges, and escorting procedures for guests. This helps ensure that visitors are authorized and monitored while on the premises.
- Security Awareness: Talk about the importance of creating a culture of security awareness among employees. Educate them about potential threats, social engineering techniques, and the role they play in maintaining physical security.
Next it is vital to understand Physical Security is closely intertwined with human nature. As a Fraud and Loss Prevention Agent I have found it is vital to in include the understanding of human behavior and motivations when designing and implementing effective physical security measures. Here are some key points regarding the relationship between physical security and human nature:
- Perception of Threat: Humans have a natural instinct to perceive and respond to threats. Physical security measures should take into account the psychological aspects of threat perception to create a sense of safety and deter potential intruders.
- Deterrence: Humans are more likely to be deterred from engaging in criminal activities if they perceive a high risk of being caught or facing negative consequences. Visible security measures, such as surveillance cameras, access control systems, and security personnel, can act as effective deterrents.
- Compliance and Rule-Breaking: Human nature is varied, and while most individuals tend to comply with rules and regulations, some may be inclined to break them. Physical security measures should consider human tendencies and vulnerabilities, ensuring that they address potential areas of non-compliance or rule-breaking.
- Social Engineering: Physical security is not solely focused on preventing unauthorized access or intrusion; it also involves protecting against social engineering techniques. Humans can be manipulated or deceived through tactics such as impersonation, tailgating (following an authorized person to gain entry), or exploiting trust. Training and awareness programs should address these risks.
- Mistakes and Human Error: Humans are prone to making mistakes and errors in judgment, which can compromise physical security. This may include leaving doors unlocked, misplacing access cards, or failing to follow proper procedures. Security measures should account for human fallibility and strive to minimize the impact of potential errors.
- Insider Threats: Human nature encompasses both positive and negative aspects. While the majority of employees are trustworthy, there is always a risk of insider threats—individuals who abuse their access privileges or exploit their position within an organization. Robust access controls, monitoring systems, and personnel vetting procedures are important to mitigate this risk.
- Collaboration and Cooperation: Human nature also includes a natural inclination for collaboration and cooperation. Physical security measures should leverage this aspect by promoting a culture of security awareness, encouraging employees to report suspicious activities, and fostering a sense of shared responsibility for maintaining a secure environment.
- Response to Emergencies: Human behavior during emergencies can vary, with some individuals experiencing panic or confusion. Physical security plans should consider human reactions in crisis situations and provide clear instructions, evacuation routes, and emergency response protocols to ensure a safe and organized response.
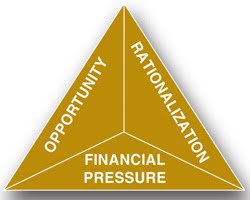
Understanding human nature and behavior is crucial in designing physical security measures that are effective, user-friendly, and aligned with the natural tendencies and vulnerabilities of individuals. By considering these factors, organizations can create a more robust and comprehensive approach to physical security. Always remenber the concept of the Fraud Triangle in your planning. The fraud triangle is a concept developed by criminologist Donald Cressey to explain the factors that contribute to the occurrence of occupational fraud. It suggests that three elements must be present for an individual to commit fraud: opportunity, pressure, and rationalization. Let's delve into each element:
Opportunity: The first element of the fraud triangle is the presence of an opportunity. This refers to the conditions or circumstances that enable an individual to carry out fraudulent acts without detection. Factors such as weak internal controls, lack of oversight, or inadequate segregation of duties can create opportunities for fraudsters to exploit.
Pressure: The second element of the fraud triangle is pressure or incentive. Financial difficulties, personal debts, addiction, or the desire to maintain a lavish lifestyle are common examples of pressures that can motivate individuals to commit fraud. These pressures create a perceived need for additional financial resources or personal gain.
Rationalization: The third element of the fraud triangle is rationalization, which is the process by which individuals justify their fraudulent behavior to themselves. They may convince themselves that they deserve the ill-gotten gains or that they are only "borrowing" the money temporarily and will repay it later. Rationalization helps fraudsters reconcile their actions with their own moral compass, allowing them to continue their fraudulent activities.
The fraud triangle suggests that all three elements must be present for occupational fraud to occur. Removing or effectively addressing any one of these elements can significantly reduce the likelihood of fraud. For instance, implementing strong internal controls, promoting ethical behavior, fostering a transparent organizational culture, and providing employees with resources to address financial pressures can help mitigate the risk of fraud.
While the fraud triangle is primarily focused on understanding the factors that contribute to occupational fraud, it can also be applied to physical security design. By considering the elements of the fraud triangle, organizations can develop effective physical security measures to deter and detect fraudulent activities. Here's how the fraud triangle can be related to physical security design:
- Opportunity: Physical security design should aim to reduce or eliminate opportunities for fraudulent activities. This involves implementing access control systems, surveillance cameras, and physical barriers to restrict unauthorized access to sensitive areas. By controlling and monitoring access, organizations can minimize the opportunity for individuals to commit fraudulent acts.
- Pressure & PS: While physical security design cannot directly address personal financial pressures or other individual motivations, it can indirectly influence them. For example, by implementing strong security measures and controls, organizations can create a deterrent effect that increases the perceived risk of detection. This, in turn, may reduce the pressure or motivation for potential fraudsters to commit illegal acts.
- Rationalization & PS: Physical security design can help shape an organizational culture that discourages rationalization of fraudulent behavior. By promoting ethical values, transparency, and accountability, organizations can foster an environment where individuals are less likely to justify or rationalize engaging in fraudulent activities.
Additionally, physical security design should take into account other human factors that may contribute to fraud. For example:
- Surveillance Systems: Deploying visible surveillance cameras throughout the premises can act as a deterrent and remind individuals that their actions are being monitored and recorded. This can discourage fraudulent behavior.
- Access Control and Segregation of Duties: Implementing proper access controls and segregating duties can help prevent collusion and unauthorized access to critical assets or information. This reduces the opportunity for fraud and increases the difficulty of carrying out fraudulent acts undetected.
- Reporting Mechanisms: Physical security design should include mechanisms for employees to report suspicious activities or potential security breaches confidentially. This encourages a culture of vigilance and enables timely detection and prevention of fraud.
By integrating principles from the fraud triangle into physical security design, organizations can create a more robust security posture that not only deters unauthorized access but also addresses the underlying factors that contribute to fraudulent behavior.